Google Pay

Get started with Google Pay
This page provides a comprehensive guide to successfully integrating Google Pay with DEUNA.
Google Pay is a digital wallet platform and online payment system that powers in-app, tap-to-pay, and website purchases. It enables users to make payments online from the web and with Android phones, tablets, and watches.
How it works
Integrating with Google Pay is significantly different from other traditional payment methods, so it's important to understand how it works before integrating with DEUNA.
You can use Google Pay for web purchases in your commercial strategy. Customers can use Google Pay for straightforward transactions while shopping on web browsers such as Google Chrome.
Purchases with a network token use a tokenized version of a card instead of transmitting card details. The process involves securely replacing the actual card information with a token and includes a dynamic cryptogram to validate and secure transactions. This method protects sensitive customer data while enabling smooth and secure payments.
Network token
A network token is a unique identifier issued by the card network (like Visa or Mastercard) and is specifically generated for secure and context-specific transactions, merchants, or devices.
The network token acts as a stand-in for the original card number, enabling secure transactions without exposing sensitive cardholder data. It is often paired with a cryptogram that protects the token against fraud.
Cryptogram
A cryptogram is a dynamic, transaction-specific code generated during a payment transaction to authenticate and secure the payment process. It is typically used in tokenized payment systems to add an additional layer of security.
The cryptogram is created by the card network or issuing bank, and is unique for each transaction. This ensures that, even if intercepted, it cannot be reused by attackers.
A cryptogram is often transmitted alongside the network token and is validated by the card network to authorize the transaction.
Why is a network token more secure?
- Dynamic security
- Traditional payments use a fixed PAN and CVV, which can be intercepted and reused.
- Network tokens pair with a cryptogram — a one-time, transaction-specific security code that cannot be reused if stolen.
- Concealed card number
- The original PAN is never exposed during transactions.
- Even if data is intercepted, the tokenized representation is useless outside its intended context.
- Revocability and lifecycle management
- Tokens can be easily revoked or replaced without affecting the underlying card.
- If a token is compromised, it is replaced without needing a new physical card.
Google Pay with DEUNA
This is the standard process for a Google Pay purchase in DEUNA:
Card tokenization
- A customer adds a credit or debit card to their Google Pay app.
- Google Pay requests a token from the bank that issued that card.
- After tokenization, the card is now "tokenized", meaning it has a unique identification number associated with it.
- Google Pay encrypts the card and makes it ready for payments.
Google Pay purchase
- At the time of sale, Google Pay sends the customer's tokenized card and a cryptogram.
- The cryptogram acts as a one-time-use password in the encryption process.
- The merchant app receives the cryptogram and the transaction information.
- The merchant app decrypts the payload from Google.
- The merchant app sends the payment token and related transaction information to a processor.
- The token is sent to a gateway that natively supports Google Pay.
Secure authorization
- DEUNA receives the encrypted Google Pay payload from the merchant app.
- DEUNA decrypts the payment token and relays the transaction information to a chosen gateway or receiver.
- The card network uses the token to retrieve the underlying card information in a secure environment.
- The card network authorizes the payment without exposing the card.
- For the authentication method of the card transaction:
authMethodinpaymentMethodDetails: DEUNA supportsPAN_ONLYandCRYPTOGRAM_3DS.PAN_ONLYsupports payment methods that Google Pay deems as non-tokenized cards.CRYPTOGRAM_3DSsupports payment methods that Google Pay deems as tokenized cards.
PAN_ONLYcredentials to Enable 3DS are returned via the Google Pay API.
Google Pay configuration
In DEUNA, you can choose between two certificate management options depending on whether your organization manages its own Google Pay credentials.
Google Pay certificate options
- Merchant-Managed: For merchants who have their own Google Pay credentials and certificates. You manage your Google Pay Merchant ID, public key certificate, and private key. Use this option if you require full control over your encryption keys.
- DEUNA-Managed: For merchants who prefer not to manage Google Pay credentials directly. DEUNA automatically generates and manages your Merchant ID and handles registration with Google. You only need to provide your merchant display name.
1. Merchant-Managed
In this mode, you manage your own Google Pay credentials and certificates. You must generate an encryption key pair and register the public key with Google before completing the DEUNA configuration.
The Merchant-Managed integration type corresponds to Google Pay's DIRECT tokenization. This is exclusively available to merchants who are PCI DSS compliant, as validated by a Qualified Security Assessor.
Keep in mind the following Google Pay guidelines:
1.1 Generate your encryption keys
Before configuring in DEUNA, you must generate a key pair and register the public key in the Google Pay & Wallet Console.
Keep your private key secure at all times. Never share it or expose it in client-side code.
Step 1: Generate a private key
The following command generates an Elliptic Curve private key suitable for use with NIST P-256 and writes it to key.pem:
openssl ecparam -name prime256v1 -genkey -noout -out key.pemOptional: View the private and public keys
openssl ec -in key.pem -pubout -text -nooutThe command produces an output similar to the following:
read EC key
Private-Key: (256 bit)
priv:
08:f4:ae:16:be:22:48:86:90:a6:b8:e3:72:11:cf:
...
pub:
04:e7:68:5c:ff:bd:02:ae:3b:dd:29:c6:c2:0d:c9:
...
ASN1 OID: prime256v1Step 2: Generate a base64-encoded public key
Run the following command to get a base64-encoded public key in uncompressed point format:
openssl ec -in key.pem -pubout -text -noout 2> /dev/null | grep "pub:" -A5 | sed 1d | xxd -r -p | base64 | paste -sd "\0" - | tr -d '\n\r ' > publicKey.txtThis produces a publicKey.txt file whose content resembles the following:
BOdoXP+9Aq473SnGwg3JU1aiNpsd9vH2ognq4PtDtlLGa3Kj8TPf+jaQNPyDSkh3JUhiS0KyrrlWhAgNZKHYF2Y=
The file content must not contain extra spaces or carriage returns. To verify this on Linux or macOS:od -bc publicKey.txt
Step 3: Generate a base64-encoded private key in PKCS #8 format
The Tink library expects your private key to be base64-encoded in PKCS #8 format. Run the following command to convert the private key generated in Step 1:
openssl pkcs8 -topk8 -inform PEM -outform DER -in key.pem -nocrypt | base64 | paste -sd "\0" -The command produces an output similar to the following:
MIGHAgEAMBMGByqGSM49AgEGCCqGSM49AwEHBG0wawIBAQQgWV4oK8c/MZkCLk4qSCNjW0Zm6H0CBCtSYxkXkC9FBHehRANCAAQPldOnhO2/oXjdJD1dwlFPiNs6fcdoRgFu3/Z0iKj24SjTGyLRGAtYWLGXBZcDdPj3T2bJRHRVhE8Bc2AjkT7nKey rotation
The rotation must be done each 25 monthes (Google rule).
Complete the following steps to rotate your encryption keys:
- Generate a new key pair following Steps 1–3 above.
- Open the Google Pay & Wallet Console while signed in with your Google Account.
- In the Google Pay API tab, under the Direct integration pane, click Manage next to your existing public key, then click Add another key.
- Paste the new base64-encoded public key into the Public encryption key field and click Save encryption keys.
- To ensure a seamless rotation, support decryption with both the new and old private keys during the transition period.
- Update the
publicKeyattribute in thePaymentMethodTokenizationSpecificationparameters in your code:
const tokenizationSpecification = {
"type": "DIRECT",
"parameters": {
"protocolVersion": "ECv2",
"publicKey": "BOdoXP1aiNp.....kh3JUhiSZKHYF2Y="
}
}- Deploy the updated code to production. From this point, new transactions are encrypted using the new key pair.
- Confirm that the old public key is no longer used to encrypt any transactions.
You must continue to support the old private key for decryption for eight days after removing the old public key.
- Once confirmed, remove the old private key.
- Return to the Google Pay & Wallet Console, click Manage next to your existing public key, click Delete next to the old public key, and click Save encryption keys.
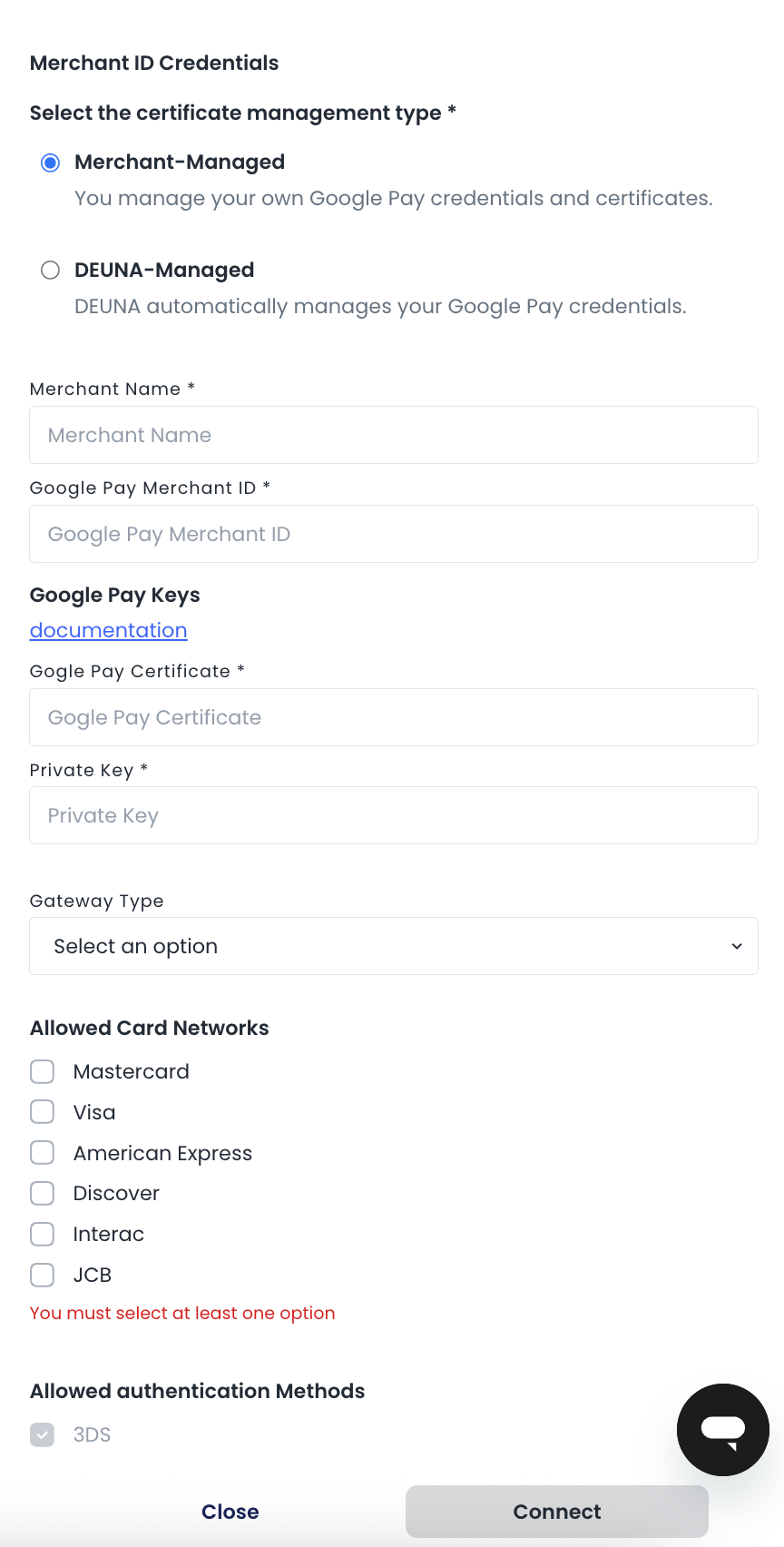
1.2 Register credentials in DEUNA
Once your keys are ready, configure the connection in the DEUNA Admin:
- Log in to your DEUNA Admin session.
- Click Connections and search for Google Pay.
- Click Connect.
- Under Select the certificate management type, select Merchant-Managed.
- Enter the following information:
- Merchant Name: A display name to identify the credential.
- Google Pay Merchant ID: Your Google Pay Merchant ID.
- Google Pay Certificate: The base64-encoded public key generated in Step 2.
- Private Key: The base64-encoded private key in PKCS #8 format generated in Step 3.
- Gateway Type: Select your gateway.
- Under Allowed Card Networks, select at least one card brand: Mastercard, Visa, American Express, Discover, Interac, or JCB.
- Under Allowed Authentication Methods, 3DS is always enabled. Optionally enable Pan Only.
- Click Connect.
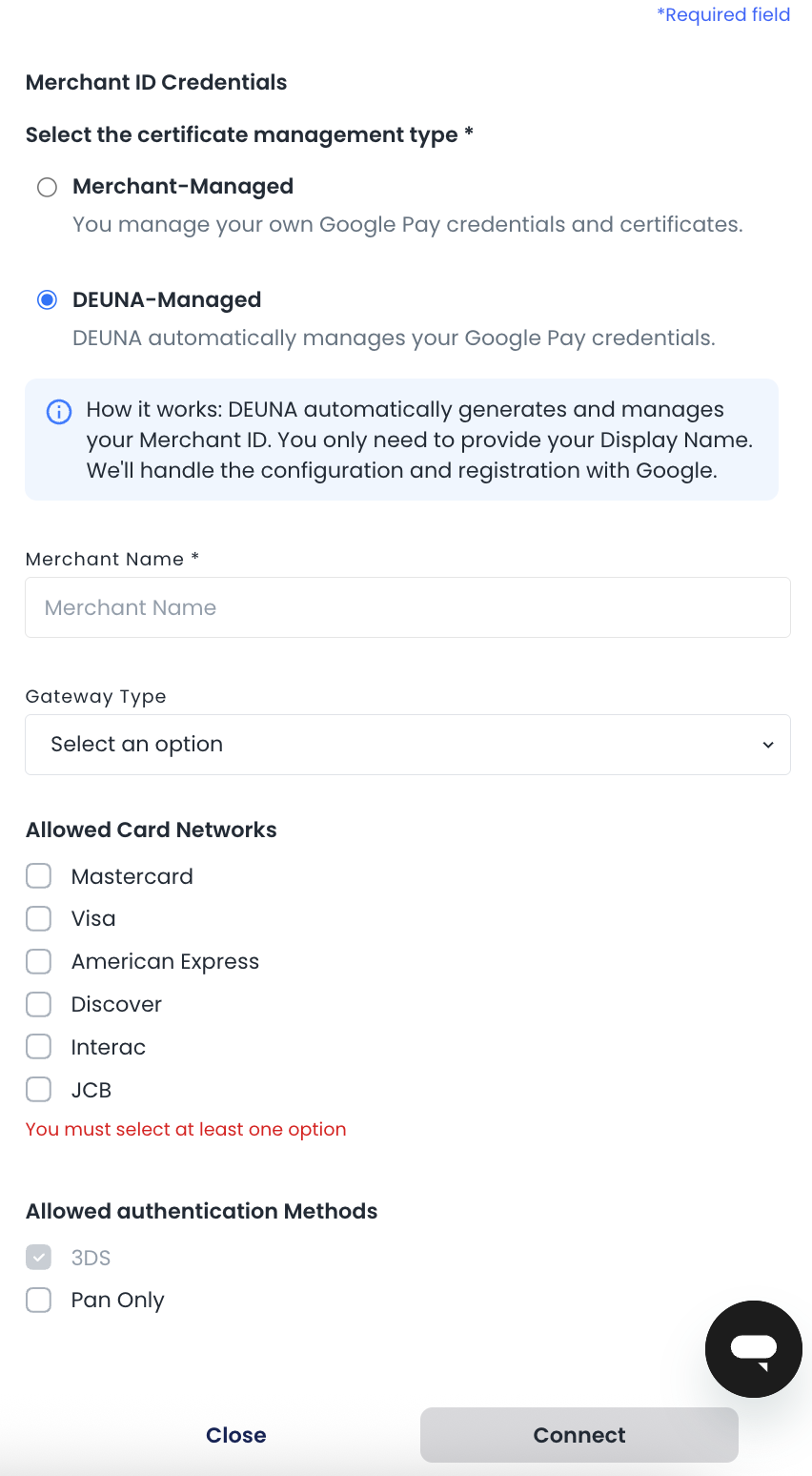
2. DEUNA-Managed
In this mode, DEUNA automatically generates and manages your Google Pay Merchant ID and handles registration with Google. You only need to provide your merchant display name.
- Log in to your DEUNA Admin session.
- Click Connections and search for Google Pay.
- Click Connect.
- Under Select the certificate management type, select DEUNA-Managed.
- Enter the following information:
- Merchant Name: A display name to identify the credential.
- Gateway Type: Select your gateway.
- Under Allowed Card Networks, select at least one card brand: Mastercard, Visa, American Express, Discover, Interac, or JCB.
- Under Allowed Authentication Methods, 3DS is always enabled. Optionally enable Pan Only.
- Click Connect.
Supported configuration
Processors
- Stripe
- Adyen
- Getnet
Countries
- MX, US and BR
Coming up:
- BBVA
- WorldPay
- Elavon
- PayU
- AMEX
- Cielo
Updated 25 days ago